OP_DUP
OP_HASH160
OP_PUSHBYTES_20
55ae51684c43435da751ac8d2173b2652eb64105
OP_EQUALVERIFY
OP_CHECKSIG
P2PKH
Pay To Public Key Hash
P2PKH (Pay To Public Key Hash) is a legacy script pattern used to "send" someone bitcoins.
It was the most common script used for locking an output to someone's public key.
P2PKH is also functionally similar to P2PK, but a P2PKH lock contains a public key hash instead of a raw public key.
Legacy Script. This is a legacy script pattern. It's still used occasionally, but P2WPKH is now the preferred choice (which works in the same way).
Usage
How does P2PKH work?
ScriptPubKey
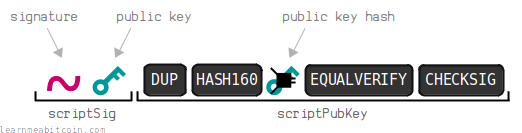
The P2PKH script pattern contains a public key hash surrounded by the following opcodes in the ScriptPubKey:
76a91455ae51684c43435da751ac8d2173b2652eb6410588acTransaction: 0b6461de422c46a221db99608fcbe0326e4f2325ebf2a47c9faf660ed61ee6a4 (Output 1)
ScriptSig
To solve this script, the owner of the hashed public key above needs to provide the original public key, along with a valid signature in the ScriptSig:
OP_PUSHBYTES_72
3045022100c233c3a8a510e03ad18b0a24694ef00c78101bfd5ac075b8c1037952ce26e91e02205aa5f8f88f29bb4ad5808ebc12abfd26bd791256f367b04c6d955f01f28a772401
OP_PUSHBYTES_33
03f0609c81a45f8cab67fc2d050c21b1acd3d37c7acfd54041be6601ab4cef4f31
483045022100c233c3a8a510e03ad18b0a24694ef00c78101bfd5ac075b8c1037952ce26e91e02205aa5f8f88f29bb4ad5808ebc12abfd26bd791256f367b04c6d955f01f28a7724012103f0609c81a45f8cab67fc2d050c21b1acd3d37c7acfd54041be6601ab4cef4f31Transaction: 40e331b67c0fe7750bb3b1943b378bf702dce86124dc12fa5980f975db7ec930 (Input 0)
The original public key provided in the ScriptSig can be a compressed public key (33 bytes) or an uncompressed public key (65 bytes).
You can use either within a P2PKH, as long as you use the same format of public key used to create the public key hash in the ScriptPubKey. For example, you can't put the public key hash of a compressed public key in the ScriptPubKey, then unlock it using the uncompressed public key in the ScriptSig (because it will not hash to the same value).
It's rare to see uncompressed public keys being used within a P2PKH, but it is technically possible.
Execution
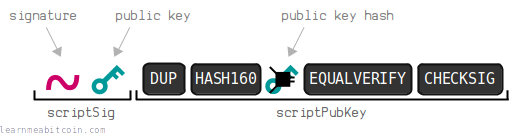
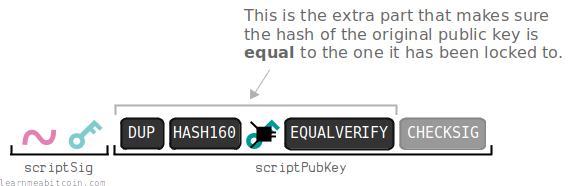
When this script runs:
- The original public key is
OP_DUPlicated and thenOP_HASH160'ed. - This hashed value is compared with the public key hash in the ScriptPubKey to make sure it is
OP_EQUALVERIFY. - If it matches, the script continues and the
OP_CHECKSIGchecks the signature against the public key, and puts anOP_1on the stack if it's valid (just like a P2PK script).
Examples
What does a P2PKH script look like?
P2PKH was the default script used by wallets when you wanted to "send" someone bitcoins up until around 2016, so you can find it in most blocks up until then (and even up until this day).
Here are some interesting transactions that use P2PKH:
-
- ScriptPubKey: 6f7cf9580f1c2dfb3c4d5d043cdbb128c640e3f20161245aa7372e9666168516 (output 0)
- ScriptSig: 12e753ef5cc30925a6eee2c457aa7f53022443ca013ea81882a6b59b69e342a6 (input 1)
- This was the first ever P2PKH transaction.
-
- ScriptPubKey: a1075db55d416d3ca199f55b6084e2115b9345e16c5cf302fc80e9d5fbf5d48d (output 0)
- ScriptSig: cca7507897abc89628f450e8b1e0c6fca4ec3f7b34cccf55f3f531c659ff4d79 (input 0)
- This was the 10,000 BTC pizza transaction.
-
- ScriptPubKey: a2bf21f6d8b7aa77c740d0374e4759791d97c0134bc918c93bae8e14879c8ecc (output 0)
- ScriptSig: faf2987fd2240d9c46575cc35c354eeca71b794c482f3cc49fba1a5f9a80808c (input 0)
- This is just a random P2PKH transaction made in 2023. I've just included it here to show that P2PKH locking scripts are still in use, even though P2WPKH (made available after the Segregated Witness upgrade in 2016) is now the more popular choice for sending bitcoins to someone's address.
Address
How do you create an address for a P2PKH script?
The P2PKH locking script pattern has been assigned its own address.
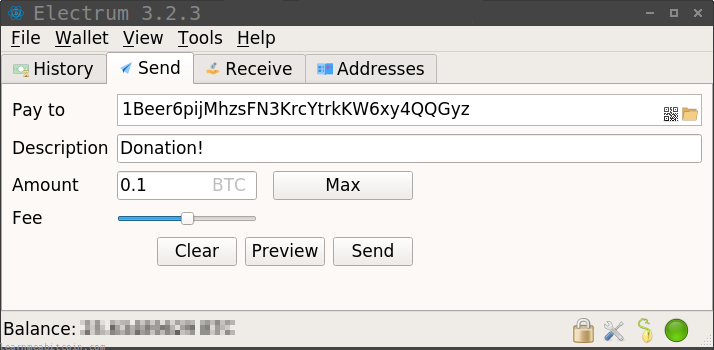
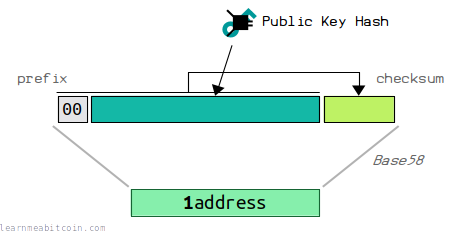
The address for a P2PKH locking script is the Base58Check encoding of the public key hash with a 1-byte prefix of 00 (mainnet) or 6f (testnet).
A P2PKH address always starts with a 1 (mainnet) or m/n (testnet).
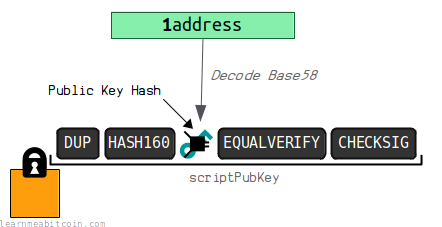
When a wallet encounters this type of address, it will decode it from base58 to extract the public key hash, then use that to construct a P2PKH locking script to be placed on the output of the transaction.
History
Why do we use P2PKH?
Why do we have P2PKH as well as P2PK? Or in other words, if P2PK does a good job of locking up bitcoins to a public key, why do we have the more complex P2PKH script?
I believe the reason goes something like this…
Satoshi wanted an easier way for people to be able to share their public keys with each other. Satoshi wanted to improve upon using public keys directly by making them:
However, the result was still pretty big:
Satoshi was probably not aware of compressed public keys at the time. This meant the address wasn't quite as short as it could be using public keys directly.
Example Address (Uncompressed Public Key)
public key (uncompressed) = 04283338ffd784c198147f99aed2cc16709c90b1522e3b3637b312a6f9130e0eda7081e373a96d36be319710cd5c134aaffba81ff08650d7de8af332fe4d8cde20 prefix + public key + checksum = 0004283338ffd784c198147f99aed2cc16709c90b1522e3b3637b312a6f9130e0eda7081e373a96d36be319710cd5c134aaffba81ff08650d7de8af332fe4d8cde2067da00eb base58 address = 13QECtNiFPXijbMZmcgaTom3pCXwHvDYTUWGtRxZN7fY24u4fG5iiqXaQz3TvuQydLrkz9L4YhcYn3khC44yQwaZme6uoXQ
Therefore, a solution for getting an even shorter address is to hash the public key first:
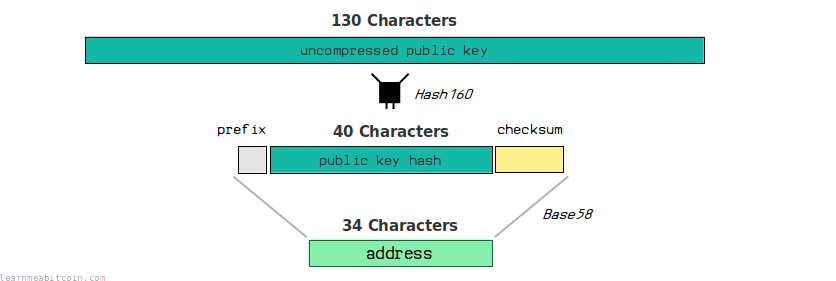
Example Address (HASH160 Uncompressed Public Key)
public key (uncompressed) = 04283338ffd784c198147f99aed2cc16709c90b1522e3b3637b312a6f9130e0eda7081e373a96d36be319710cd5c134aaffba81ff08650d7de8af332fe4d8cde20 hash160(public key) = bc73550c1612ee81155d29254217cbd60084a6d1 prefix + hash160(public key) + checksum = 00bc73550c1612ee81155d29254217cbd60084a6d1691c58b9 base58 address = 1JBSCVF6VM6QjFZyTnbpLjoCJTQEqVbepG
A hash function is useful for creating a short representation of some data.
So there we have a much shorter version of our public key (an address) that we can easily share with other people.
Now, in terms of the locking script logic, the only thing we have to do to make this work is to change the locking mechanism so that we lock an output to the public key hash instead.
Therefore, when we come to unlock it we provide the original public key, and the hash of that will be checked before carrying on with the signature verification as normal:
It's a bit more complex from a programming perspective, but this allows for the use of shorter and more convenient addresses for sending and receiving bitcoins.
So in summary, I believe Satoshi ultimately had usability in mind for Bitcoin, and that's why they came up with P2PKH.
Would we still use P2PKH if Satoshi knew about compressed public keys?
Maybe, maybe not. Good question.
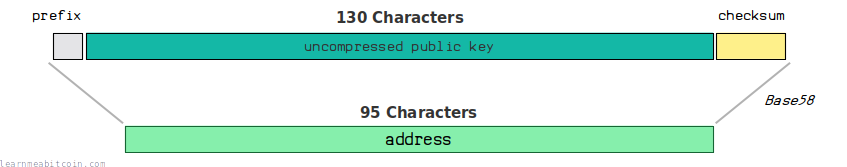
If you base58 encoded a compressed public key you would get an address that is 51 characters long (as opposed to the 34 characters you get by hashing it beforehand), so there may not have been as much as an incentive to hashing before creating an address:
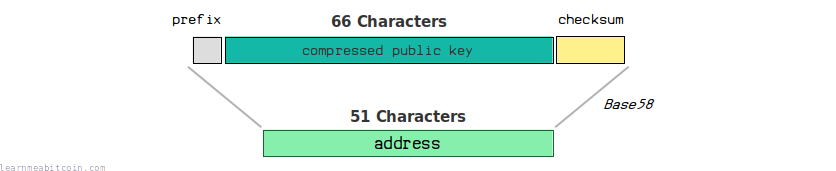
And 51 characters isn't too bad for passing around.
Example Address (Compressed Public Key)
public key (compressed) = 02283338ffd784c198147f99aed2cc16709c90b1522e3b3637b312a6f9130e0eda prefix + public key + checksum = 0002283338ffd784c198147f99aed2cc16709c90b1522e3b3637b312a6f9130e0eda85f983ee # (prefix+checksum) base58 address = 15CCDBsovXLij5wtGe5joZNymEZSnQhpfXjbxybMMybrMqnmBUy
Nonetheless, P2PKH had become the standard for sending and receiving bitcoins by this point, so that's why we have stuck with it.
Still, it would have been simpler to have used P2PK with addresses made from compressed public keys.